
Simple, Fast, and Secure Identity Security
Detect and respond to identity threats in real time — without complex IAM projects.
Leading companies trust Identity Rules to understand and reduce their identity risk



0%
of breaches involve compromised credentials
0%
of IAM projects fail due to their complexity
The problem isn't cybersecurity.
It's not understanding the risk in your access.
- More users, applications, and privileges increase risk without you even realizing it.
- Orphaned accounts and excessive access remain a critical vulnerability.
- Traditional IAM solutions are slow, expensive, and difficult to implement.
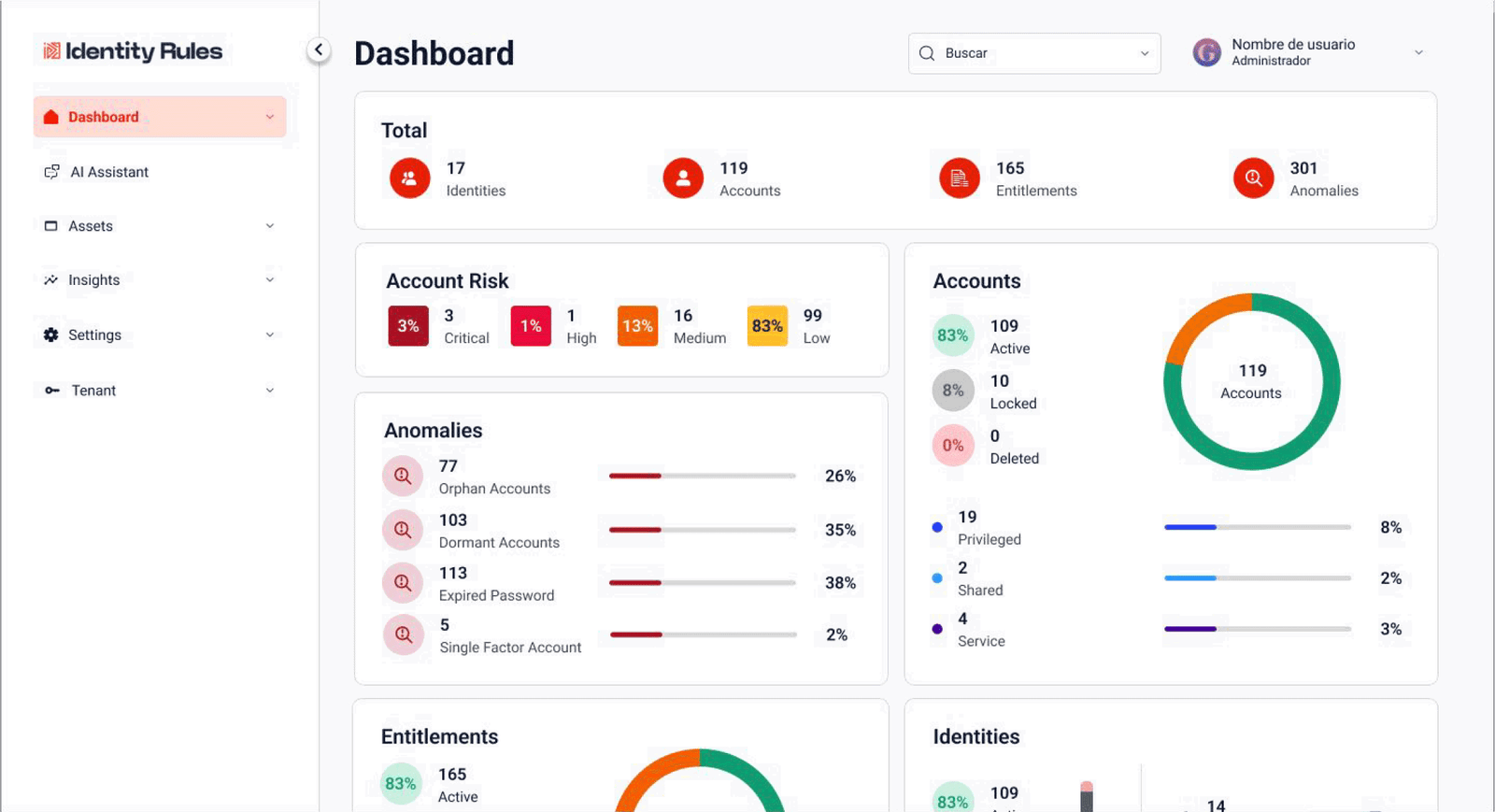
Identity Rules IAM On Demand
Identity Rules offers a comprehensive, on-demand solution for managing identities, access, and privileges without the complexity of traditional projects. It can be deployed in days, not months, with a multi-tenant, scalable, cloud-ready architecture accessible to any type of business.
What you can do with Identity Rules
🔐 Centralized visibility of identities and access.
Understand who has access to what, with what privileges, and in what context.
⚙️ Rapid integration with your ecosystem
Easily connect with Active Directory, Entra ID, Google Workspace, and more.
🧠 Real-time risk detection
Identify unauthorized access, excessive privileges, and anomalies before they become incidents.
📊 Actionable intelligence and reports
Gain clear insights for audits, compliance, and decision-making.
☁️ Flexible Model (SaaS or On-Premise)
Adapt to your architecture without friction or complex dependencies.
Why are identity rules different?
Intelligence, not just management
You don't just manage access: you understand the risk behind it.
No technical complexity
Agile deployment without the need for lengthy projects or complex development.
Rapid Implementation
Implementation up to 10 times faster than other platforms
Scalable by design
Works in hybrid environments and grows with your organization.
Cost Optimization
Reduces operating costs and avoids unnecessary investments in traditional IAM projects.
Real-time Visibility
Turns identity data into useful context to detect and respond to incidents.
Measurable results from the first month
Key Benefits
Facilitates compliance with standards such as ISO 27001, PCI, SOX and NIST
Total control and visibility over identities and privileges
Scalability without the need for additional infrastructure
Up to 80% value with only 20% of the implementation effort
Immediate reduction of
the risk of unauthorized access
Measurable results from the first month
Key Benefits
Facilitates compliance with standards such as ISO 27001, PCI, SOX and NIST
Total control and visibility over identities and privileges
Immediate reduction of the risk of unauthorized access
Scalability without the need for additional infrastructure
Up to 80% value with only 20% of the implementation effort
Real-world use cases
Visibility and diagnosis of identity risks.
Gain a clear view in days of who has access to what and with what level of privilege.
- Identification of orphaned accounts, unnecessary access, and excessive privileges
- Early detection of risks before they become incidents
- Solid foundation for making informed decisions without relying on manual processes
- First real step toward an identity governance strategy
Continuous compliance without operational friction
Meet regulations without increasing your team’s workload.
- Automatic evidence and complete traceability for audits.
- Alignment with ISO 27001, NIST, PCI, and other standards
- Reduction of human error in reviews and certifications
- Greater confidence from auditors, clients, and stakeholders
Control of privileged access
Reduce risk where it has the greatest impact: critical access.
- Identification of oversized or unnecessary privileges
- Continuous monitoring of sensitive access.
- Detection of anomalous behavior in critical accounts
- Improved governance and control of privileged identities
Agile response to access incidents
Act fast when it really matters.
- Real-time detection of unauthorized or risky access
- Significant reduction in mean time to response (MTTR)
- Clear context for SOC, IT, and compliance teams
- Faster investigations thanks to identity intelligence
Testimonials
“We gained complete visibility into access in less than a week.”
CISO, Regional Financial Company
“We went from months to days in understanding our identity environment.”
IT Director, Industrial Group
Make identity management SIMPLE
Start with what matters most: visibility. You can't protect what you can't see. Identity Rules allows you to understand your identity risk and act before it becomes an incident.
Security for your business, wherever you are.
Multi-tenant support (SaaS or On Premise Deployment)
Integrations with Active Directory, Linux, Entra ID and Google Workspace