
Simple, Fast, and Secure Identity Security
The first Identity Security platform designed for SMB and accessible to any type of company
Companies that trust us to protect their digital identity



0%
of the breaches involve compromised credentials.
0%
of IAM projects fail due to
the complexity
of their implementation and management.
The complexity of managing identities and access and detecting threats
- Organizations face an increasingly regulated and digitized environment.
- Multiple applications, users, and roles increase the risks of unauthorized access, orphaned accounts, and excessive privileges.
- Implementing traditional IAM solutions is often costly, time-consuming, and complex.
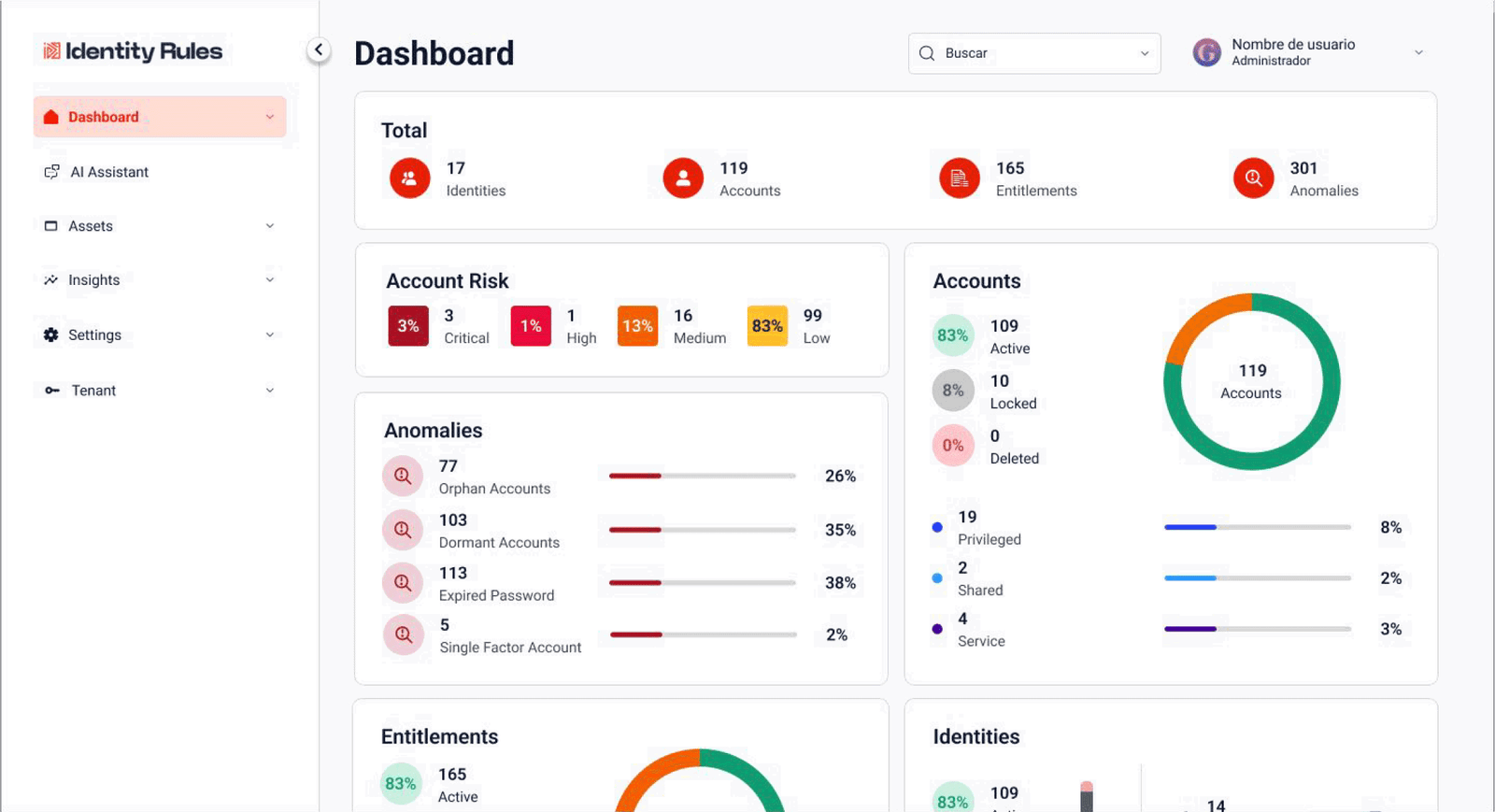
Identity Rules IAM On Demand
Identity Rules offers a comprehensive, on-demand solution for managing identities, access, and privileges without the complexity of traditional projects. It can be deployed in days, not months, with a multi-tenant, scalable, cloud-ready architecture accessible to any type of business.
Key Features
🔐 Centralized Identity and Access Management
⚙️Native integration with Active Directory, Entra ID, Google Workspace, Oracle DB, SQL Server, Linux, and more
🧠 AI-powered analytics for risk detection in accounts and access
📊 Automated and AI-powered reports for regulations and compliance
☁️ 100% managed and secure SaaS model
🏢 Support for On-Premise Deployment
What Makes Us Different?
AI
AI-driven investigation and identity threat analysis.
No-Code
Fast deployment with minimal technical knowledge required.
Speed
Implementation up to 10× faster than traditional competitors.
Scalability
Flexible SaaS and on-premise deployment options.
Cost Efficiency
Lower upfront and operational costs.
Unique Insights
Real-time identity intelligence for incident detection.
Measurable results from the first month
Key Benefits
Compliance with ISO 27K, PCI, and SOX.
Full control and visibility over identities and privileges.
Scalability without additional infrastructure.
80% of functional value with only
20% implementation effort
Immediate reduction of
unauthorized access risks.
Measurable results from the first month
Key Benefits
Compliance with ISO 27K, PCI, and SOX.
Full control and visibility over identities and privileges.
Scalability without additional infrastructure.
80% of functional value with only 20% implementation effort
Immediate reduction of unauthorized access risks.
Use Cases
Initial visibility of accounts and access
- The first tangible step toward a mature IAM model.
- Immediate risk reduction from unmanaged accounts.
- Rapid diagnosis of access, privileges, and identity risks.
- A solid foundation for audits, certifications, and identity governance initiatives.
Regulatory compliance
- Continuous compliance with ISO 27001, ISO 27017, NIST, and LFPDPPP.
- Complete evidence and traceability for audits.
- Reduced operational effort and human error.
- Greater confidence for customers, auditors, and regulators.
Privileged account management
- Reduced risk of privilege abuse.
- Proactive control of critical access.
- Time savings in audits and access reviews.
- Stronger trust in identity governance processes.
Faster incident response
- Significant reduction in MTTR for access-related incidents.
- Improved audit control and traceability.
- Better coordination between SOC, IT, and compliance teams.
- Proactive prevention through early detection of anomalous access.
Testimonials
“With Identity Rules, we achieved full access visibility in less than a week.”
CISO, Regional Financial Company
“Implementing IAM used to take months; with Identity Rules, it took just days.”
IT Director, Mexican Industrial Group
Make identity management SIMPLE
Request a free demo and discover how Identity Rules helps you protect identities and access with a simple, agile, secure, and scalable model.
Security for your business, wherever you are.
Multi-tenant support (SaaS or On Premise Deployment)
Integrations with Active Directory, Linux, Entra ID and Google Workspace